Serverless is coming, and the basics never really go away!
Lambda, automation, and the no infra future
In five to ten years virtual machines will be as much relics as mainframes are today. Forrest Brazeal recently wrote an article detailing a coming IT job apocalypse, and how the only way to avoid your job becoming redundant was to develop your skillset. He isn’t wrong. Even a newb like me can see that the way of the future is through technologies like Lambda, Azure Functions, and infrastructure-LESS services.
This is scary. As the future always is.
And really stinking cool. Instead of worrying about hardware, network maintenance, and virtual machine infrastructure: we worry about our applications. What does it mean for business? It means that new products get pushed out faster. Customer input is easier to ingest and integrate with products. Licensing costs for expensive services like Enterprise Operating Systems or SQL disappear. It means that the security surrounding your applications changes, for the better.
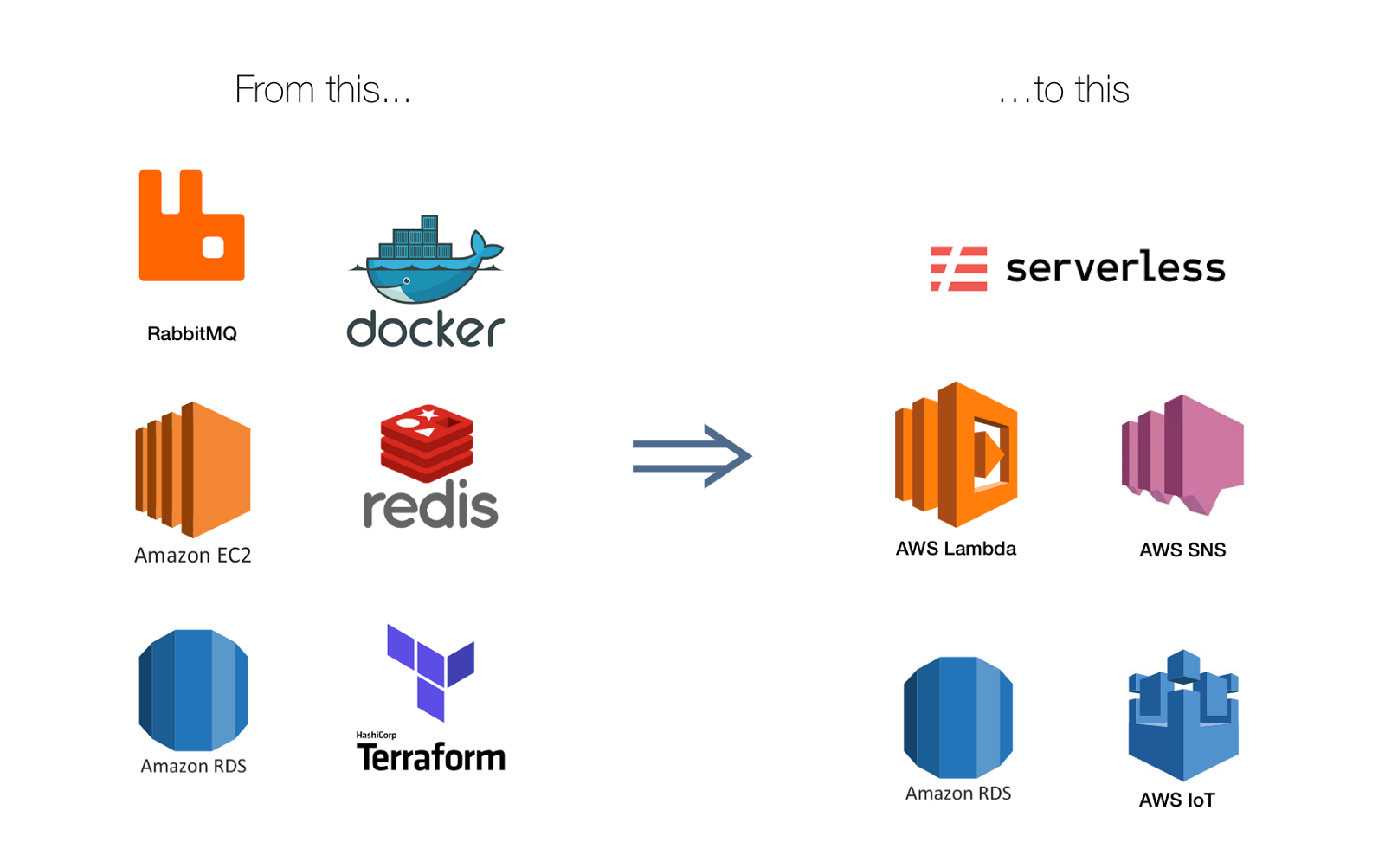
The decrease in footprint size of a Virtual Machine infrastructure hosting your IIS server, coupled with an app server, joined with your database, attached to your domain, running on your network…. to just running point in time functions through something like Lambda? Dramatic to say the least.
There are still a ton of concerns; from securing your actual cloud infrastructure to ensuring regulatory requirements are met, but the actual application is looking so much healthier and resilient than before. The threats remain, though.
DVSA
The Damn Vulnerable Serverless Application (DVSA) was created by Protego. They also head up the OWASP Serverless Top 10 which, similar to OWASP’s other projects, tracks the top ten threats to serverless applications.
DVSA is a purposefully vulnerable, misconfigured web application. The application is a video game store that hosts an order platform and payment portal. It stores PCI and PII. Both of which are not well secured or managed in the stores backend. The application has barely any restrictions and a script kiddie could pwn this app in minutes. In fact, DVSA has instructions on how to do just that.
Setting up DVSA is simple, but the instructions are included in soundless videos. To deploy, navigate to the “Serverless Marketplace”, or the AWS Serverless Application Repository. There are currently around 450 different application waiting to be deployed in your environment. Search for DVSA, and BAM! Launch it and you’re off to the races.
Once the application is set up you can start going through the app and poking holes in it. Protego provides ten lessons that cover some of the OWASP Serverless top 10. The top 10 serverless threats are extremely similar to the basic web application threats. In fact, they are the exact same at the moment, but with an addendum: “Other Risks to Consider”.
- Denial of Service
- Denial of Wallet
- Insecure Secret Management
- Insecure Shared Space
- Business Logic/Flow Manipulation
Conclusion
None of those threats are actually unique to serverless applications. They can each be exploited in traditional web application architectures, even when hosting in the cloud. Which really means, securing these applications is not recreating the wheel. We are using the same tactics we already use.
Properly sanitize your data. Use your vulnerability scanners. Provide security training to users. Practice role based access control and least privilege. The basics. They still apply to this new realm of serverless technologies.