Almost a week after starting, I have finally finished indexing book 2. I am not sure if I underestimated the amount of time that I need to finish these study sessions, or if I’m just slow, but creating this index is taking much longer than I initially thought. However, after book 2 I am up to around 160 index entries, which I have no idea whether that is normal or not.
On the flipside, tonights study session highlighted several major areas that I didn’t know I had such a gap in.
SMB Exploitation and Understanding
SMB seems to be the bane of Windows existence in recent years. WannaCry and NotPetya annihilated the industry through the use of SMBv1, and it continues to be seen all over the world today. The major themes from the recent text that I covered surround utilizing SMB to enumerate Windows domain information.
This includes finding more domain users to target, or password spray against. This includes the extremely complicated (insert sarcasm) net use command. The scariest part about this enumeration method, is that regardless of SMB version, this is the intended manner of SMB. This is one of those times that function overrules security, I guess. Or else at this point rearchitecting that protocol would be way too large of a monumental effort.
This section also covered rpcclient and smbclient in Linux, and how to utilize those to enumerate domain information from a Windows box.
A lot of the defenses from this particular vector revolved around proper network segmentation and firewall defenses. Make sure you don’t have a flat network, every port is accounted for, and you may not have a bad time.
IP and TCP/UDP Header Architecture
This is definitely one of those areas that I struggle in, because it is pure memorization. I have a decent memory for stuff I read, but rote memorization sucks. Flash cards suck, quizlet cards suck. Yet sometimes you just have to bite the bullet.
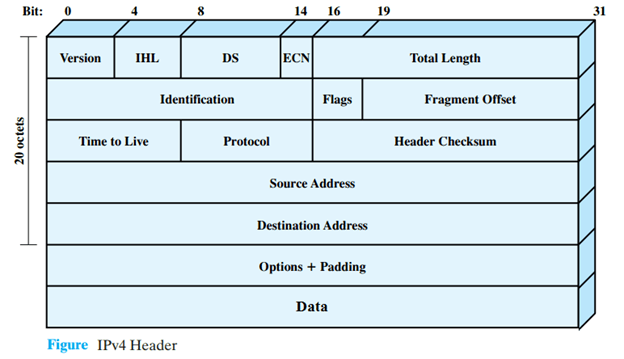
Network headers aren’t covered super heavily in this course. I remember Jham talking about how some of the other SANS courses do cover headers heavily. Those include actually spotting attacks based upon malicious flags. In this class, and the GIAC, I think that the main area is going to be just understanding what TTL is, and how it’s used. Plus knowing that headers contain source and destination IP’s.
TTL is specifically called out in multiple areas, and goes in depth about how TTL works and why it works the way it does. I was pretty surprised to learn that tracert uses TTL to determine next hop location. I always assumed the program just did some magic behind the scenes… which isn’t totally wrong.
Log 2 Summary
In summary. This is tiring. I do feel rushed to cram as hard as I ever have, but I think that is because I want that 90% score. Juggling this between family, work, and just personal care is pretty challenging, but hopefully will be 100% worth it.